Docker logging to AWS CloudWatch

One of the ways to log Docker containers is to use the logging drivers. These drivers log the stdout and stderr output of a Docker container to a destination. The awslogs driver allows you to log your containers to AWS CloudWatch, which is useful if you are already using other AWS services and would like to store and access the log data on the cloud. While our Docker is running on AWS EC2 instance it looks as best option. When logs are in CloudWatch you can monitor and analyse using alarms and dashboards.
In this article we will assume you already have Docker running on AWS EC2 instance. Next steps describes how to set up the integration between your Docker and AWS CloudWatch.
Setting Up AWS
Before you start logging to CloudWath, you need to make sure that application running inside AWS EC2 instance are able to communicate with AWS. This means that you need a role with a policy that allows for the writing of events to CloudWatch, then attach this role to the EC2 instance.
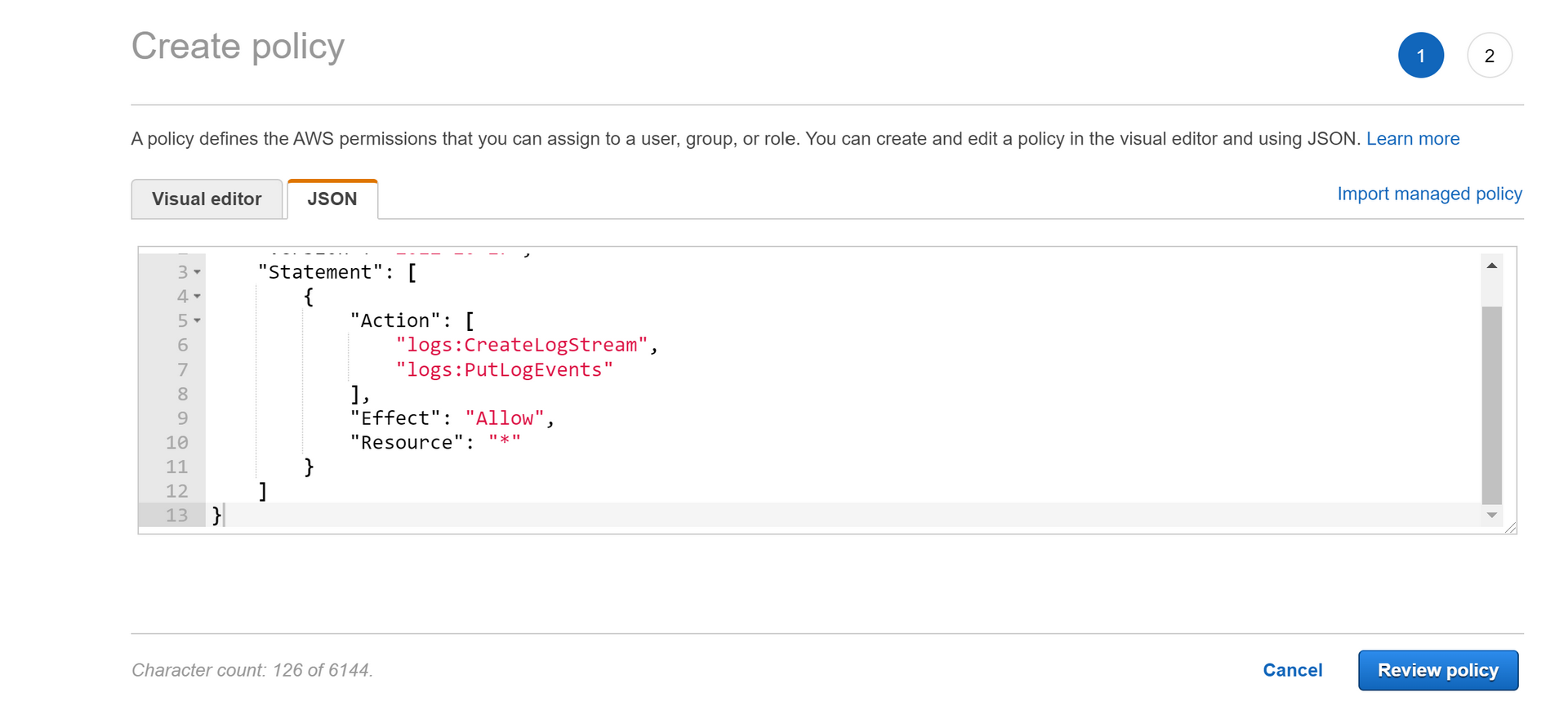
Creating policy
First, you will need to define a new policy. So just open IAM console, select Policies from the menu on the left, and use JSON editor to create policy which enables only writing logs to CloudWatch. Then name the policy meaningfully for example CloudWatchLogsWrite
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"logs:CreateLogStream",
"logs:PutLogEvents"
],
"Effect": "Allow",
"Resource": "*"
}
]
}
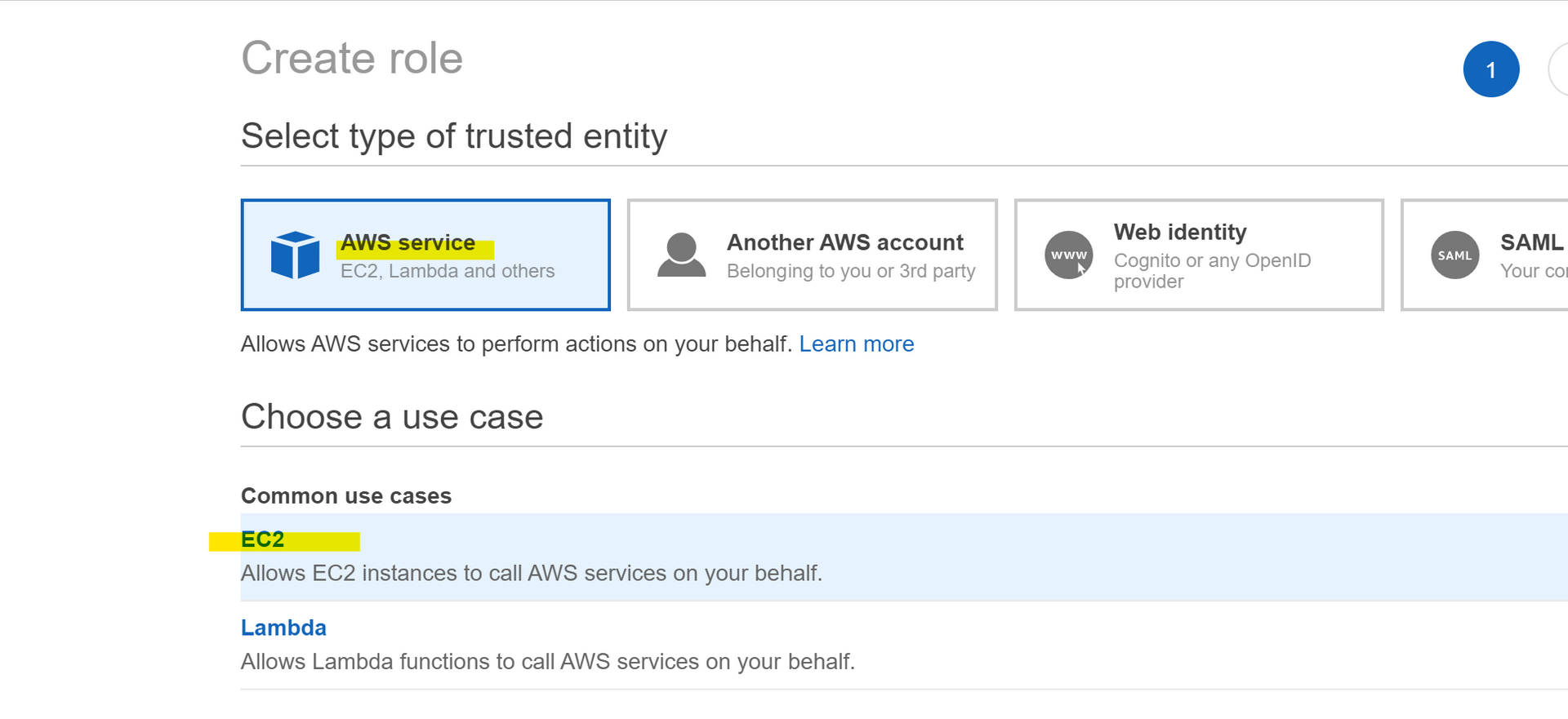
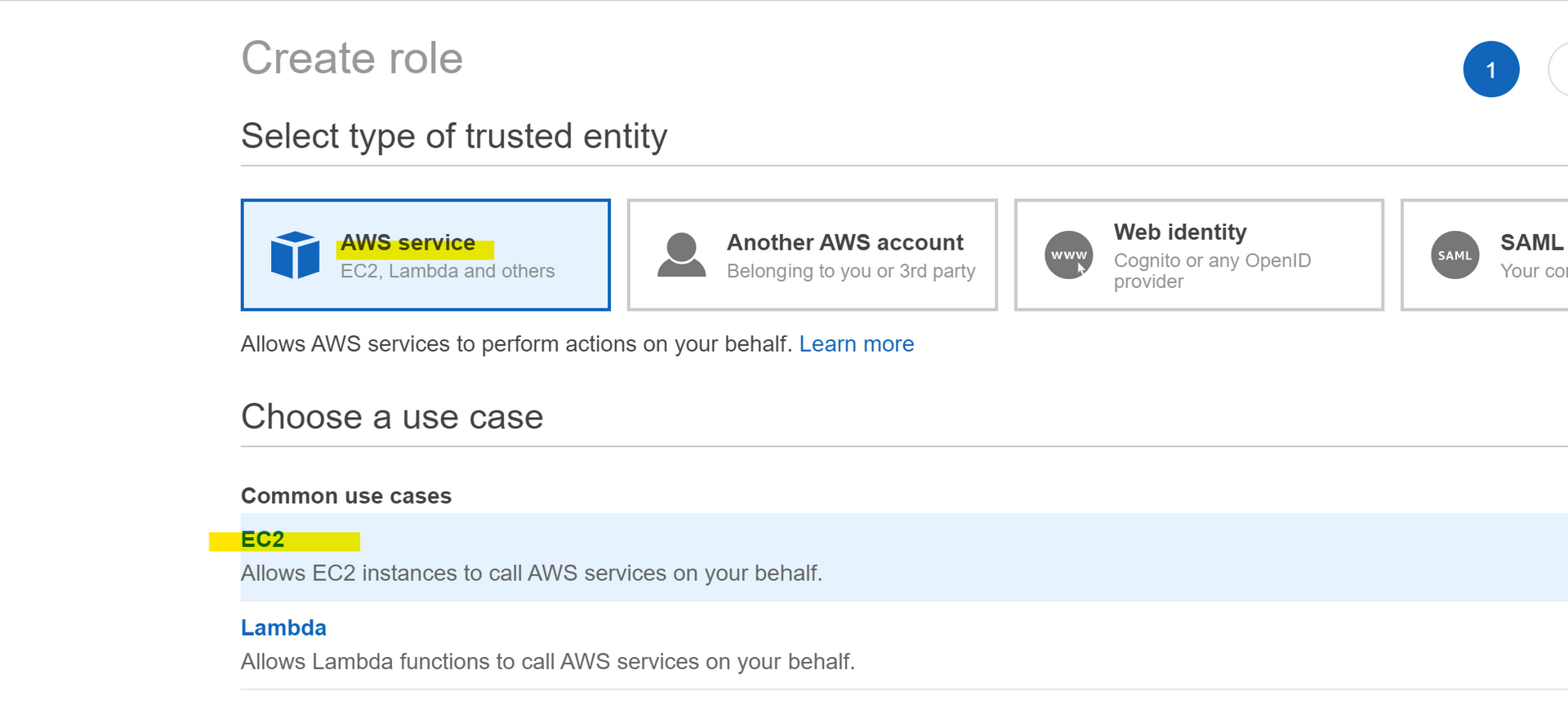
Creating role
So open the IAM console, from left tree select roles, then start creating new role for EC2. While this is the common use case just select EC2 and go next step.
You have to continue to attach permission policy to a role. Search for previously created policy let say CloudWatchLogsWrite then select te policy and go to review and finally name this role meaningfully for example EC2WriteCloudWatchLogs.
Attaching role
Next step is to attach previously created role to the running EC2 instance. It will make allow applications running inside the instance to write logs to CloudWatch.
Click the search at top left of the AWS console to find for EC2 service. Then open the EC2 instance management console and select the instance you want attach the policy.
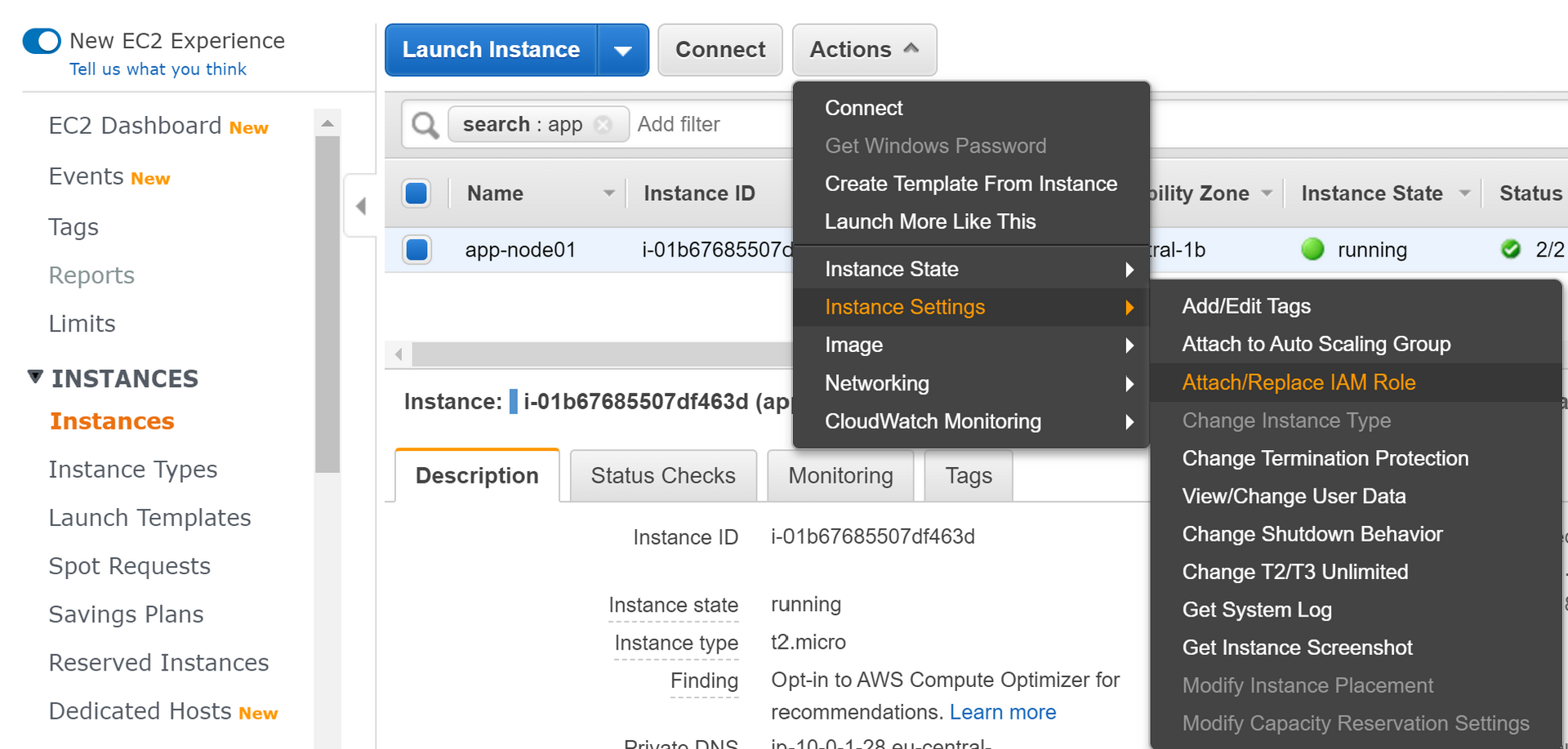
Click instance actions button, within menu go to Instance Settings and Attach/Replace IAM Role. Then select role you have already created let say EC2WriteCloudWatchLogs and apply to finish.
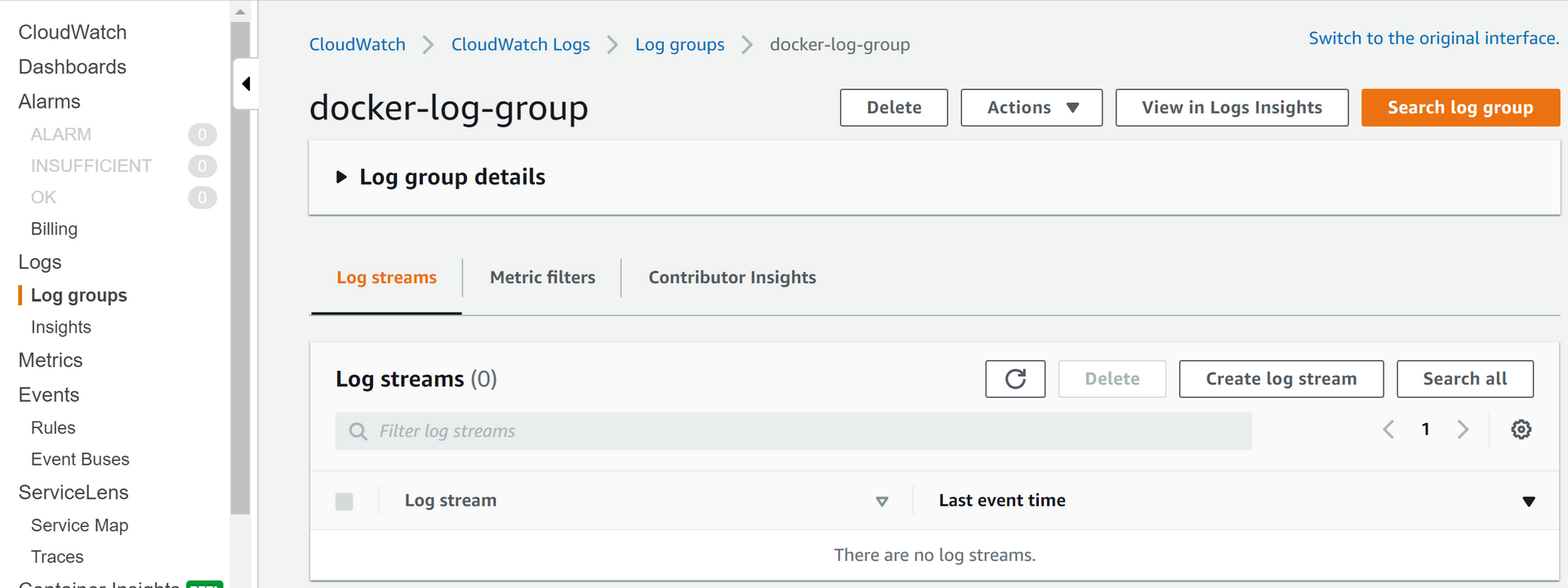
Creating log group
Open CloudWatch console and find Log groups inside Logs menu. Click create new log group and name it for example docker-log-group. Within this new log group, create a new log stream let say app-name-log-stream. Make note of both the log group and log stream names — you will use them when running the container.
Running container
Now that Docker has the correct permissions to write to CloudWatch, it’s time to test the logging capability. Just use docker run command with the –awslogs driver parameters:
docker run -it --log-driver="awslogs" --log-opt awslogs-region="eu-central-1" --log-opt awslogs-group="docker-log-group" --log-opt awslogs-stream="app-name-log-stream" ubuntu bash


